Corrupted Micro SD Card freezes computer
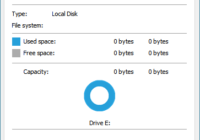
If inserting a corrupted Micro SD Card, that you need to recover data from, freezes your computer, then this kind of puts you into a catch 22 situation. For recovery software to work the card needs to be detected and ID correctly. As long as it doesn’t you will be unable to recover your data.… Read More »